CORE and AI Operations - A Match Made in Mt. Olympus
- Dennis Hackney
- 13 hours ago
- 3 min read
Taking a closer look at the Mythos platform from the CORE lense.

Recently, on the podcast, I took a deep dive into the unauthorized breach of Anthropic’s Mythos platform. For those who missed it, Mythos is a highly specialized, agentic AI model trained specifically for cybersecurity operations, capable of full-scale autonomous vulnerability discovery and exploitation. While the thought of an autonomous AI iterating payloads in real-time against legacy operational technology is terrifying, the defensive potential of such a platform is immense. Today, I will explore how a frontier AI model like Mythos could be integrated into the Cost-effective, Operational, Reliable, and Efficient (C.O.R.E.) Technology Security methodology to supercharge our critical infrastructure defense.
Let's break down this integration across the fundamental practices of the C.O.R.E. program.
C.O.R.E. Inventory (Categorization)
The first step in C.O.R.E. is achieving a 100% accurate asset inventory by capturing Organization, Technology, and Process characteristics, most notably the 3Cs: Criticality, Confidentiality, and Capability to set priorities. Mythos can be leveraged to autonomously ingest and validate the C.O.R.E. Tags applied to each technology. By automatically analyzing the Attack Vector and Connectivity characteristics (whether Physical, Local, Adjacent Network, or Network), Mythos could instantly prioritize assets based on their capability to control the physical world.


C.O.R.E. Remediation
C.O.R.E. Remediation involves architecture secure configuration, endpoint configuration management (via DISA STIG or CIS benchmarks), and software vulnerability patching. Because Mythos acts as an autonomous agent, it could perform active vulnerability scanning across every major operating system and evaluate security gaps. Instead of relying on manual security benchmarking, Mythos could autonomously evaluate new patches on technology function, determine operational impacts, and dynamically rewrite configurations to apply security benchmarks without breaking legacy systems. Or for those leary of automation, just flag high risk assets, instantly.


C.O.R.E. Detection
Detection involves identifying technology attributes to provide visibility into potential cyberattacks across New, Mature, and Old technologies. Integrating Mythos into the Security Information and Event Management (SIEM) environment would revolutionize the C.O.R.E. Threat Intelligence Engine. Mythos could correlate MITRE ATT&CK tactics, techniques, and procedures (TTPs) with the localized C.O.R.E. Tag data points (Sector, Region, Location). By observing network traffic and event logs, Mythos could act with the speed of software to detect anomalies that human operators might dismiss as routine degradation, or miss completely.
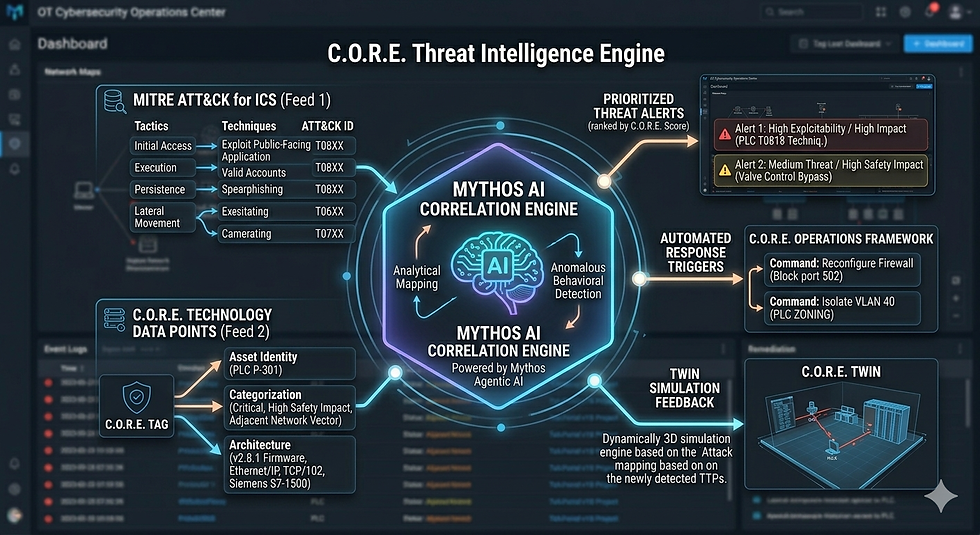

C.O.R.E. Decision-Making
Effective security decisions in the C.O.R.E. methodology must be Boolean (yes or no) and evaluated against specific business factors: Executive, Financial, Legal, Technical, and Operational. By calculating the C.O.R.E. Technology Prioritization Score (combining Impact and Exploitability using a stabilized measurement equation from CVSS metrics), Mythos could automate the cost-versus-benefit analysis. When a request is made, such as moving a SCADA server to the cloud, Mythos could rapidly weigh the counter-perspectives and issue a calculated decision, rationale, and actionable next steps.


C.O.R.E. Operations
C.O.R.E. Operations centralizes Inventory, Remediation, Detection, and Decision into the Security Operations Center (SOC). Here, Mythos would act as the ultimate Security Orchestration and Automated Response (SOAR) engine. If an intrusion is detected, Mythos can rapidly command the reconfiguration of Layer 7 firewalls, implement quarantine protocols, or restrict routing across internal VLANs to prevent lateral movement.


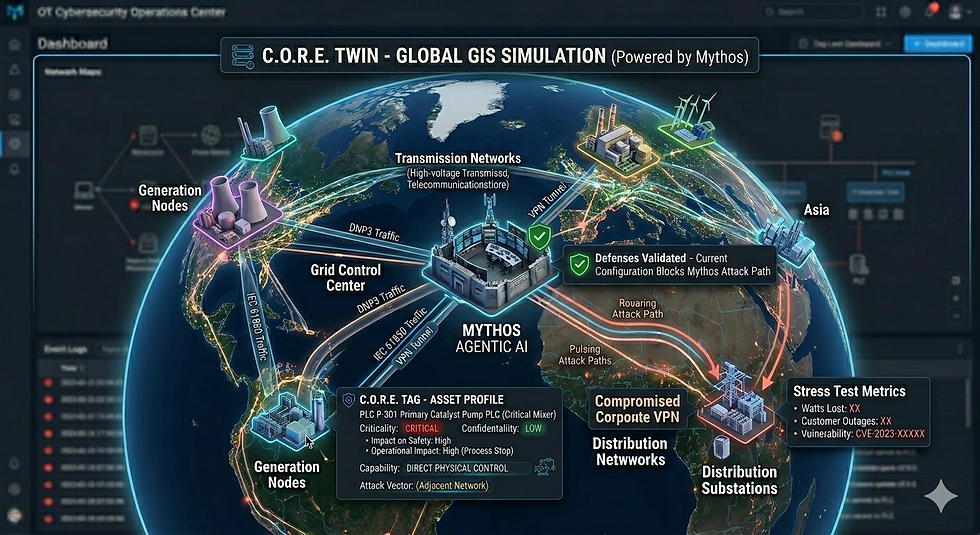
C.O.R.E. Twin (Digital Twins in Security Operations)
The C.O.R.E. Twin is a virtual model that simulates the physical operational environment, enabling proactive planning and attack path analysis. This is where a model like Mythos is best utilized. By pointing Mythos at the C.O.R.E. Twin, which provides lightweight mirroring of actual device configurations and connectivity, defenders can unleash Mythos to conduct cyber defense stress testing. Mythos can attempt zero-day exploits, escalate privileges, and map attack paths within the Twin, allowing the organization to validate boundary protections and test new security technologies safely without impacting physical production.

Conclusion
As we noted on the podcast, we cannot simply out-compute an AI. However, by strategically integrating autonomous agents like Mythos into a structured, fundamentally sound framework like C.O.R.E., we can out-architect them, ensuring our critical infrastructure remains resilient, reliable, and secure.
— Dennis Hackney, Ph.D. OT Cybersecurity Leader | Creator of CORE | Host of CyberSecureOT
Transparency Statement: AI tools were utilized to assist in drafting and structuring portions of this article. The author maintains full responsibility for the final content and its intended message. This content is provided for informational purposes only and does not constitute formal professional or legal advice.



Comments